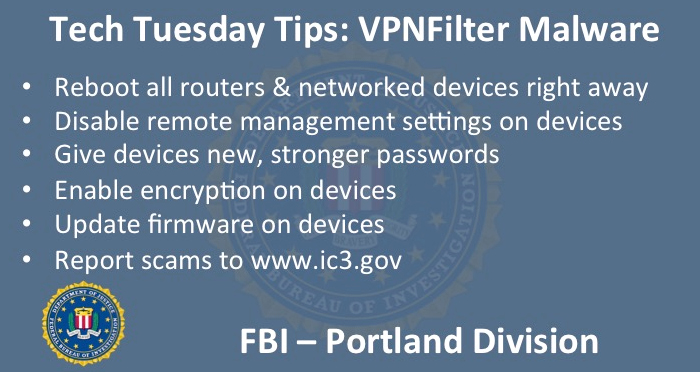
Welcome to the Oregon FBI’s Tech Tuesday segment. This week, building a digital defense against a new threat targeting your home or business network.
The FBI’s Internet Crime Complaint Center – or IC3.gov – has just released a new, urgent warning for those who use routers either at home or in a small business. Cyber actors working out of foreign countries have compromised hundreds of thousands of these routers and other networked devices using what’s called “VPNFilter malware”. This malware has the ability to watch the traffic that is moving through the router – stealing data, executing commands, blocking network traffic and even “bricking” the device. Once a device is “bricked” it can’t be recovered and is forever unusable.
This VPNFilter malware comes in three stages, and it’s important to understand the difference. The first stage has a persistent presence – meaning that it simply sits there and waits for the command and control server to download new modules.
Once the malware downloads the second stage, it can start exploiting the device and doing harm. There are also stage three modules that can make the malware both harder to track and better at stealing critical information.
The FBI is recommending that both home users and businesses immediately reboot your routers and networked devices. This will disrupt stages 2 and 3. It is important to note that stage 1 will remain on the device and may call out again to the command and control server to re-load stage 2. By re-booting, though, you are creating a break that will allow the FBI, internet service providers, and other partner agencies to try to identify and remediate the damage done by this malware.
This break also allows users to set up their own digital defenses. Owners should disable remote management settings on devices and make sure that the device has new, strong passwords. Do not use default user IDs and passwords – that’s an open door to hackers. Also, enable encryption when able and upgrade the device with the latest available version of firmware.
For more information on the VPNFilter malware go to https://www.ic3.gov/media/2018/180525.aspx or https://www.justice.gov/opa/pr/justice-department-announces-actions-disrupt-advanced-persistent-threat-28-botnet-infected